With cyber threats rising, the Securities and Exchange Commission (SEC) recently introduced new rules requiring prompt disclosure of significant cyber incidents. This has created a challenge for public companies, who must now report major breaches within four business days.
This blog post explores how Uptycs can provide a strategic partnership for rapid compliance.
SEC cybersecurity rules
The SEC introduced its new cybersecurity disclosure rules in July, marking a significant shift in how public companies are required to manage and report cyber incidents. At the core of these rules is the mandate for timely disclosure, demanding that public companies report significant cyber incidents within just four business days.
The rules extend beyond mere notification, emphasizing the need for detailed disclosure about the nature and impact of the cyberattacks, as well as the company's preparedness and response strategies. By mandating such comprehensive and timely disclosures, the SEC aims to ensure that investors and stakeholders are fully informed about the cybersecurity risks and incidents that could affect their investment decisions.
Swift incident detection is essential
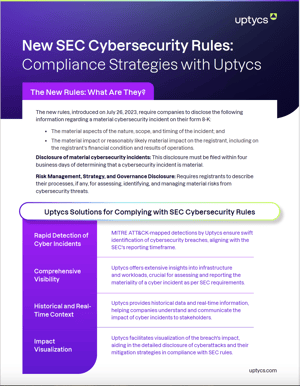
The ability to detect cyber threats quickly is crucial in combating them. Uptycs offers a unified tool suite that leverages real-time scanning and the MITRE ATT&CK framework to identify threats and map them against known attack techniques. This proactive approach is vital for meeting SEC reporting deadlines and minimizing the impact of cyber incidents.
Comprehensive visibility into cybersecurity posture
Assessing the materiality of a cyber incident requires deep visibility into an organization's infrastructure and workloads. Uptycs provides an expansive view of cybersecurity posture, from developer laptops to code and cloud. This visibility helps accurately evaluate the severity of incidents and inform disclosure strategies in line with SEC guidelines.
Harnessing historical and real-time data for effective communication
Understanding the full spectrum of a cyber incident requires both real-time data and historical context. Uptycs' platform offers a rich repository of historical cybersecurity data, allowing organizations to trace the evolution of threats and their mitigation efforts. This comprehensive reporting aligns with the SEC's objective of transparent and informed communication with stakeholders.
Visualizing the Impact for Accurate Disclosure
Effectively communicating the impact of cyber incidents is crucial for SEC compliance. Uptycs provides impact visualization tools that enable organizations to articulate the extent and implications of cyberattacks in a clear and detailed manner. This helps stakeholders, including investors and regulators, to fully understand the incident and comply with the SEC's requirements.
Download our Infographic: Uptycs Solutions for Complying with SEC Cybersecurity Rules
Uptycs: A strategic partner for SEC compliance
Complying with the SEC's new cybersecurity rules may seem challenging, but it is possible with the help of Uptycs. Uptycs’ unified suite of cybersecurity solutions detects and analyzes cyber incidents in real-time while effectively communicating their impact. This strategic approach ensures compliance and strengthens the overall cybersecurity posture. Partnering with Uptycs is a forward-thinking and resilient strategy for companies committed to protecting stakeholders and maintaining investor trust in the face of evolving threats and regulatory landscapes.
Uptycs offers a robust framework for organizations navigating the SEC's new cybersecurity rules. Rapid detection, comprehensive visibility, and effective communication strategies are essential for timely and accurate disclosure of cyber incidents. By embracing these strategies, companies can demonstrate their commitment to transparency and investor protection in the digital age.t and comply with the SEC's requirements.