While endpoint agents have always tried to be the eyes and ears for security, an overabundance of them may be degrading security rather than improving it. A 2017 survey from Barkly and Ponemon Institute finds that companies have as many as seven different agents running on each endpoint, while at the same time, three out of four report still having difficulty managing endpoint risk.
Other security solutions require agents for compliance, data leakage, vulnerability and patch management, network security solutions, systems management, and more. The industry has gone agent crazy, it seems, resulting in significant performance issues, escalating licensing costs, conflicts with other services running on the endpoints, maintenance headaches, difficulties for upgrades and certification issues, and more.
The problem of too many agents mirrors the problem of too many separate security solutions. This Cisco Newsroom article, summarizing their 2017 Annual Cybersecurity Report, states that 65 percent of organizations are using from six to more than 50 security products, increasing the potential for security effectiveness gaps. Individual security products have spread across the enterprise in the attempt of solving point problems or addressing specific security concerns or even requirements. The evolution of security as a perimeter to security everywhere has resulted in organizations having a broad portfolio of solutions. At the same time, evolution of computing environments to encompass on-premise, public cloud and private cloud with a range of physical and virtualized resources has expanded attack surfaces and complicated the task of security.
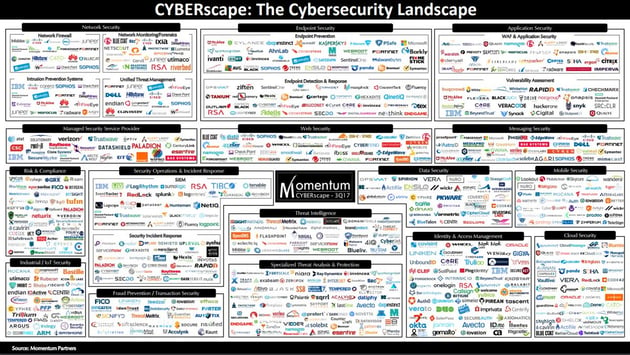
The time has come to change the siloed approach to security. Single-purpose, proprietary, closed-model solutions are becoming counterproductive and too difficult to sustain. Many CISOs are now asking whether their organizations can support yet another standalone solution. Organizations need a comprehensive security platform that can reduce the number and type of agents, and enable sharing of data for various functions. They need to streamline the number of separate dashboards and management controls to ease the job of running, interpreting and maintaining security systems. They need to correlate and integrate data to enable viewing “the forest for the trees” to find and stop bad actors, and minimize or eliminate damage.
Agents should be able to collect a wide range of system data and run analytics that should feed multiple functions and solve an array of problems and challenges. Black-box processing should give way to clear, understandable processing that can enable multiple functions. A flexible, powerful platform should provide modularity of solutions and functionality that can scale with the organization’s growth, the evolution of problems and challenges, and the availability of new approaches to solve issues.
It’s not impossible to do.
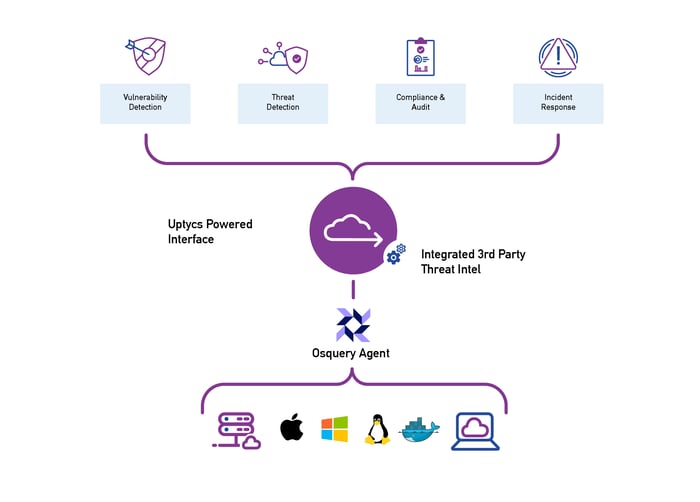
Osquery is offering a new approach to accessing insight across operating systems, computing environments, and data sources. (more on osquery here) Growing adoption of the universal, open source agent is ushering in the disruption needed to support a unified approach to enterprise security.
We're aiming to deliver on the promise of osquery at scale by pairing the agent with a centralized management console with a powerful analytics engine, historical lookback/ full system state recreation, and helpful views of that data to solve multiple security challenges. (We've laid out our vision in pretty picture form below.) If you're interested in learning more, grab a demo. We'd love your feedback.