With weightier compliance penalties, ever-deepening cybercrime, and rapid adoption rates of public or hybrid cloud, financial services companies must pay closer attention to cloud compliance and stop treating it in a vacuum.
A 2018 study conducted jointly by Deloitte and the Financial Services Information Sharing and Analysis Center (FS-ISAC) raises the question of, “What does ‘good’ look like when it comes to cybersecurity at financial services companies?” The answer, concludes Deloitte experts, is not at all obvious: “The answer may be difficult to determine in the midst of a constantly changing threat landscape, and at a time when shifting business priorities and exponential technology forces are changing how many organizations approach management of cyber risks.” Compliance in the cloud is no longer simply a matter of one-dimensional audits or a segmented compliance officer or team.
Similarly, compliance goes beyond employing encryption for data at rest or in motion.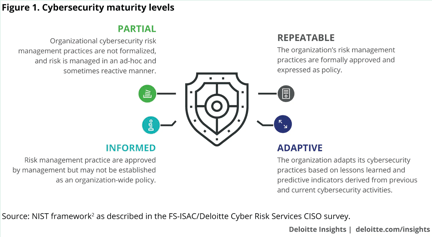
True cloud compliance can only be considered through an integrated view of data security, cybersecurity and risk management. Each discipline—with its people, processes and technology—carries considerations that must be aligned together rather than individually or not at all. To build a cloud compliance program, one needs a fundamental understanding of each of the three areas, and a full consideration of exposures or risks through the “lens” of each. Each has a set of benchmarks and evaluation criteria that can be (NIST, CIS) or must be (PCI, FedRamp, SOC 1, GDPR) adopted to ensure measurable compliance. Exposure must be a combined view of the organization and all involved partners or vendors.
Data Security
Most financial services companies now understand that security and compliance are inseparable attributes and programs that must be considered together. The more traditional elements of data security dwell on encryption and associated key management. Common thinking insists that as long as data is encrypted and the keys are managed, security can be assured. Such a view misses the reality and prevalence of credential theft and the commandeering of users’ computers to gain access to encrypted or segmented resources.
Data security must encompass not only encryption and key management but also authorization and authentication. Critical elements for review include LDAP for directory information services and definitions of who has access to what, Single Sign-On technologies across all fixed and mobile platforms as well as connected applications, and multi-factor authentication schemes and solutions.
Cybersecurity
Cybersecurity, or the combination of network security and cloud security, must be evaluated in total to understand the entire attack surface, where vulnerabilities may exist and what level of protection or detection exists. While equal or identical security infrastructure is unlikely on premise as well as in the cloud, organizations will want to ensure consistent policies across both. Organizations should also periodically evaluate or audit the security directly delivered by cloud infrastructure providers and also the available resources to support one’s own security solutions.
Risk Management
Both security and compliance need to be considered in terms of risk management. While compliance can be achieved and certified, security is never perfect, if only because threat actors and means are constantly changing. Continuously assessing risk, therefore, is essential and will help determine or evaluate policies. Consider a continuum of risk, ranging from high to low.
Accepting high risk generally means more open access, freedom and ease of use. Low risk will mean highly restricted access and greater difficulty and complexity in implementation, assessment and use. Fundamentally, risk management combines continuous monitoring, analyzing and auditing of events in your environment for traces of vulnerability or suspicious activity.
[Related article: How osquery helps secure your cloud with these two critical CIS benchmark controls.]
Money Isn’t Everything
While adequate funding is important for security infrastructure, assessment and operation, it is not the sole determinant of quality or level. The study from Deloitte mentioned earlier admits, “Money is not the sole criterion of cybersecurity effectiveness.” People, processes, policies and technology all pay essential roles, and these are only partially influenced by monetary spending.
In addition, despite the best use of these four factors, the continuous and rigorous review of data security, cybersecurity and risk management together play a crucial role in achieving and maintaining effectiveness. There is certainly a cost component to such a review, but the practice of integrating these three areas is based not on cash, but on an expertise and understanding of its necessity across all levels of an organization.
Avoiding a Vacuum
The security and compliance challenges facing today’s financial services companies are enormous. What does good look like? Good is security and compliance reviewed together through the combined lenses of data security, cybersecurity and risk management that is continuously monitored and evaluated against benchmarks or standards. The sum of these provides a more realistic and insightful view of security and compliance than the individual parts.