As the demand for cybersecurity professionals steadily increases, so do the qualifications necessary to equip the field with the most advanced prospects. With the ability to showcase an applied mastery of skills and to train entry-level professionals posited as the two main goals of most cybersecurity certifications, the determining factor should lie within which will make you the most competitive.
Certifications validate knowledge of best practices, and as their value directly correlates with job preparedness in the field, having a certification to magnify your arsenal of skills can be what takes your career to the next level.
Contents
5 Most Searched Cybersecurity Certifications
Notable Specializations to Consider
Our Certification Path of Choice
5 Most Searched for Cybersecurity Certifications
According to a search performed on 300 cybersecurity certifications across three popular job boards, LinkedIn, Indeed, and Simply Hired, the 5 certifications below prove to continuously pique the interest of job posters in the cybersecurity field, who in June of 2021 contributed to the largest year over year increase in pool of employers listing them as requirements they are actively hiring for.
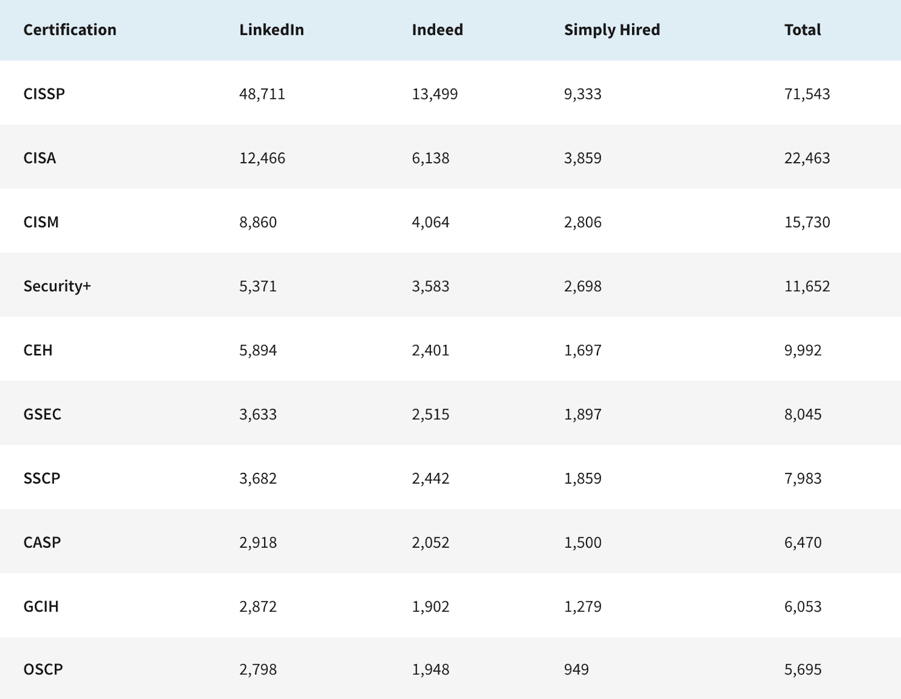
Number of US Job search results for each certification when searched on June 10, 2021. Performed by Coursera.
Certified Information Systems Security Professional (CISSP)
- One of the most esteemed and sought after certifications in the industry, CISSP's general and vendor-independent nature makes it applicable to a wide variety of set-ups. Covering the domains of Access Control, Cryptography, Telecommunications, and Networking, many IT organizations consider this certification an essential requirement for network security.
- Requirements - Prerequisites include prior experience of 3-5 years in two of the eight domains of the CISSP Common Body of Knowledge (CBK).
Certified Information Systems Auditor (CISA)
-
CISA is a specialization designed for auditors. While not generally required outside of large compliance organizations, it remains widely recognized and demonstrates the ability to accurately assess vulnerabilities, report on compliance issues, and institute security controls within an organization. Covered domains include Information Systems Auditing, IT Management and Governance, and Protection of Information Assets.
-
Requirements - Prerequisites include 5 years of experience in IT or IS audit, control, security, or assurance. (In some cases a two or four-year degree can be substituted for one or two years of experience).
Certified Information Security Manager (CISM)
-
Considered a top credential for IT professionals in enterprise-level applications for developing the best organizational security practices, CISM is designed for security managers. CISA is a level above CISM, and affords security aspirants with the ability to demonstrate distinguished information security management. Along with experienced managers, CISM is ideal for professionals who may not have security backgrounds but are thrust into security management roles.
-
Completion of the CISM certification equips credential holders with advanced skills in Security Risk Management, Program Development and Management, Governance, and Incident Management and Response.
-
A CISM certification is valid for three years upon completion and credential holders are required to pay an annual maintenance fee.
-
Requirements - Prerequisites include at least five years of experience in information security management to take the CISM exam. You can substitute two years of this requirement with general information security experience, and can waive one to two years with another certification in good standing or a graduate degree in an information security-related field.
Security+ (SEC +)
-
Known as an exceptional starting point for beginners, CompTIA Security+ validates the baseline skills necessary to perform core security functions. IT concepts include Network Threats and Defense Techniques, Effective Security Policies, Network and Host-based Security Practices, Disaster recovery, and Encryption Standards and Products. The security+ exam covers areas of threats and attacks, architecture and design, risk management, and cryptography.
-
Requirements - There are no prerequisites for taking the Security+ exam, but it’s recommended that professionals have a CompTIA Network+ certification and two years of experience in IT administration with a focus on security.
Certified Ethical Hacker (CEH)
-
Proactive in nature and offensive in function, CEH teaches security aspirants how to think and act like a hacker. Ethical hacking, or white hacking, red team, and penetration testing, is performed in an effort to uncover vulnerabilities before malicious players do. CEH concepts include an in-depth view of hacking technologies, latest vulnerabilities, information security laws, and standards.
-
Placed in real-time scenarios, exposed to hacking techniques, and taught how to scan, hack, and protect their systems from the same, students of the CEH certification yield a considerable edge against penetration testing jobs.
-
Requirements - The CEH exam requires two years of work experience in information security or the completion of an official EC-Council training.
Notable Specializations to Consider
Offering a variety of highly respected security specializations, SANS’s GIAC certifications should be at the forefront of any specialization consideration. GCIH, GCFA, GCIA, GPEN, GSLC, and GSEC include valuable curricula suited for incident handlers, forensic analysts, intrusion analysts, and penetration testers, among others.
Uptyc’s Certification Path of Choice
With the acknowledgement of the myriad of specializations, career paths, and similar kinds of certifications available today, it's important to note there is no one exact entry point when beginning or advancing your career in the cybersecurity field.
For beginner’s, we’d recommend either SEC+ or CEH, followed by CISSP, and then a SANS specialization. A cloud related certification such as AWS Security would succeed this path well, too.
For the mid-level to advanced tier of cybersecurity professionals, SANS has a well-respected and valuable variety of specializations available.
Candidly stated but equally valuable, while certifications provide the parameters and applied definitions that demonstrate understanding and proficiency in each realm of today's cybersecurity field, being able to show your work to an employer on a platform like Github can sometimes be just as powerful.
To Read More about Best Practices and Fundamentals, Check Out Our Cloud Strategy Guide Below.