Endpoint Security
Leave no endpoint left uncovered
Attackers often target endpoints—especially developer laptops—because they know that’s where valuable credentials and data reside. Uptycs offers comprehensive endpoint security and compliance capabilities in a single solution.
Deep visibility and control for
server and laptop assets
Multiple security controls, one solution
Achieve all your security and compliance requirements in a single solution with Uptycs features like file integrity monitoring, intrusion detection, malware detection, software asset inventory, and vulnerability scanning.
- Meet key security controls required for NIST 800-53, PCI, and SOC 2
- Cut down on agent bloat that can perturb systems
- Improve staff productivity with only one solution to learn
More than
traditional EDR
Uptycs includes a number of endpoint security capabilities you won’t find with traditional EDR tools. Offering advanced allowing you to:
- View detection logic and engineer custom detections
- Run YARA rules against real-time process and file events
- Take real-time actions including carving files, running scripts, isolating hosts, blocking IPs, and more
- Monitor sensitive folders with file integrity monitoring (FIM)
- Report on organization’s exposure to newly disclosed threats
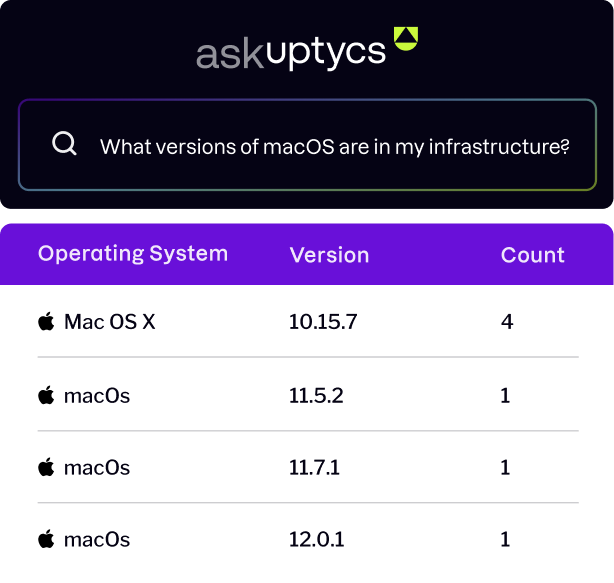
Query your
endpoint fleet
like a database
Building on and extending open-source osquery technology, Uptycs equips organizations with visibility into their endpoint fleets.
- Answer questions during threat hunting, investigations, audits, and more
- Run live and historical queries on a single system or across a fleet
- Use standard SQL; no need to learn proprietary query languages
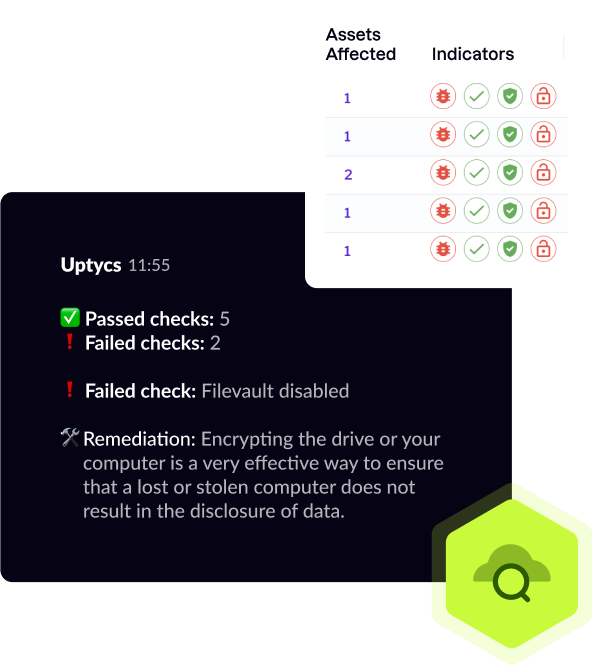
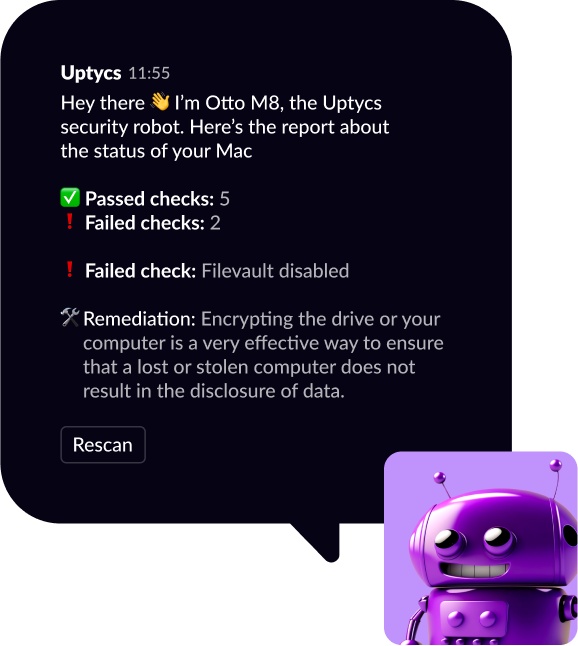
Enlist users in defense
Uptycs includes a friendly automated Slack bot, “Otto M8,” that alerts users to misconfigurations and other security issues on their devices. Otto M8 will be on hand to:
- Help users keep their devices up-to-date and secure
- Provide users with rationale and remediation steps
- Enables users to re-scan their device to confirm successful remediation
Your all-in-one solution for endpoint security, compliance, and vulnerability management
Uptycs provides you with unprecedented visibility across your endpoint fleet for threat detection and response, asset inventory and insight, audit and compliance, vulnerability scanning, and more.
Best-in-class
EDR
Detect, block, investigate, and remediate malicious behavior across macOS, Linux, and Windows platforms.
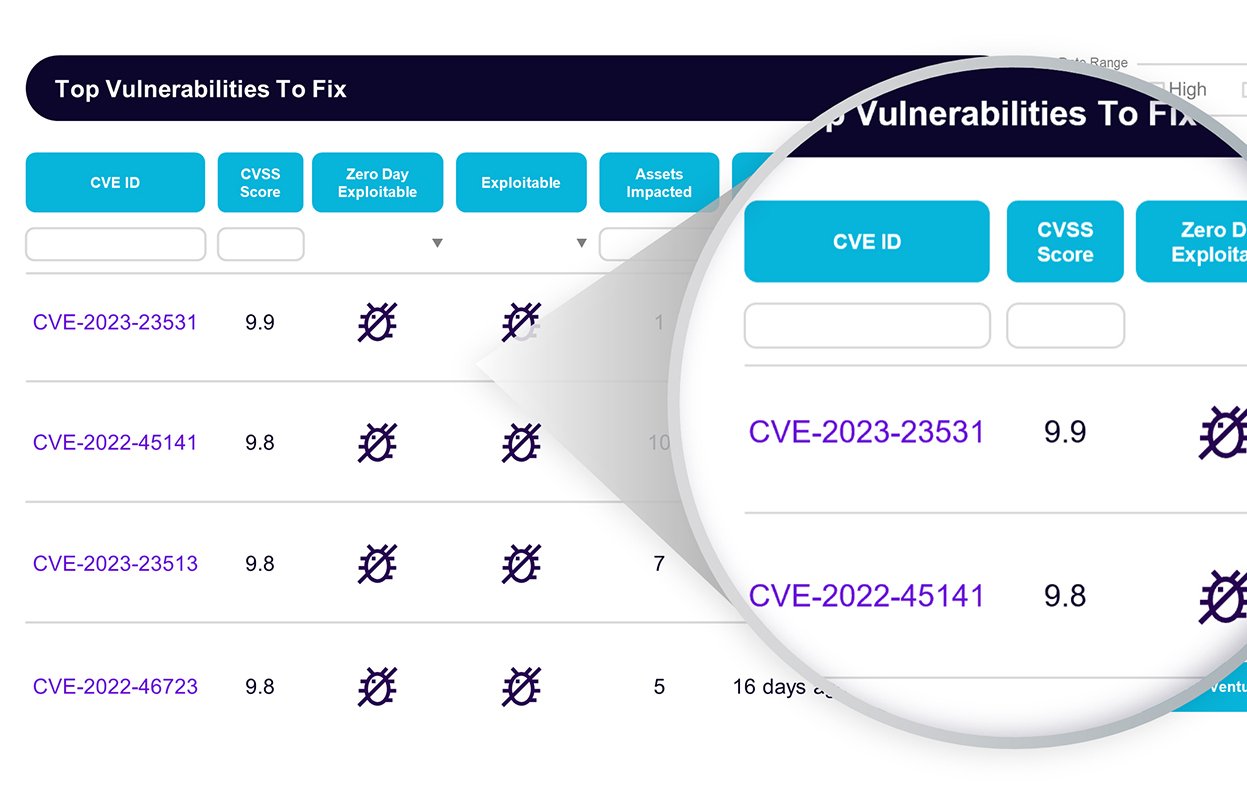
Vulnerability scanning
Answer questions fast and with confidence. Inventory vulnerable packages across your fleets and decide which systems to prioritize.
Compliance & audit
Monitor and report on all major compliance standards with flexible checks. Easily gather evidence needed for auditors and vendor assessments.
Why industry leaders
choose Uptycs
“Uptycs was deployed on a large scale as a key component of our security posture.”
Comcast
Vice President IT Security“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs has been instrumental for our FedRamp authorization and ISO 27001 certification.”
Grant Kahn
Director, Security Engineering Lookout“Uptycs helps me sleep better at night.”
Sean Todd
CISO Pay Near Me“Uptycs contextualizes threat activity across K8s, cloud services, and laptops. We've dramatically shortened our threat investigation time.”
Anwar Reddick
Director of Information Security Greenlight Financial“Uptycs provides us with a comprehensive view of our environment without the need for log shipping or other data collection methods.”
Cloud Security Engineer
Top 10 Internet Site“I would not want to do security anywhere without this level of visibility.”
Steve Shedlock
Incident Response Team Lead SEI“Everything you want to know is as easy as querying a database. It’s fantastic.”
Security Engineer
E-learning Company“Product works great, is inexpensive, zero Dev complaints about slowing down systems (IYKYK), and they've added every feature I've asked for.”
Security Operations Manager
Business Services Company"Clean interface, very good visibility across assets, and their team is open to feedback."
Manager, Information Security
Finance Industry"A unified view from which we can quickly ask and answer security questions across our environment."
Chris Castaldo
CISO Crossbeam“A major game changer for heavily used hosts (40k requsts per second). Running safely within one of the largest cloud environments on the internet. ”
Uptycs Customer
"Uptycs simplifies investigations and saves time—about 30% per investigation.
Sean McElroy
CSO Lumin Digital“If threat actors try to evade detection Uptycs captures those events”
Security Engineer
Large Telecom Company“Blazingly fast. 0.7 seconds from execution to detection, and 1.6 seconds from execution to case management alert.”
Security Engineer
Global Payment ProcessorUptycs provides actionable runtime threat and vulnerability insights and a flexible threat hunting capability.
Uptycs Customer
Director, Information Security Financial“Monitoring containers for Exploit/Mining Activity can be easily traced compared to other apps”
Security Engineer
Telecom Company“For so many issues, our answer is ‘Go to Uptycs.’”
Director of Security Operations
Enterprise Logistics Company“Uptycs enables us to make risk-based decisions.”
Chris Castaldo
CISO, Crossbeam“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs was deployed on a large scale as a key component of our security posture.”
Comcast
Vice President IT Security“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large Enterprise“Uptycs has been instrumental for our FedRamp authorization and ISO 27001 certification.”
Grant Kahn
Director, Security Engineering Lookout“Uptycs helps me sleep better at night.”
Sean Todd
CISO Pay Near Me“Uptycs contextualizes threat activity across K8s, cloud services, and laptops. We've dramatically shortened our threat investigation time.”
Anwar Reddick
Director of Information Security Greenlight Financial“Uptycs provides us with a comprehensive view of our environment without the need for log shipping or other data collection methods.”
Cloud Security Engineer
Top 10 Internet Site“I would not want to do security anywhere without this level of visibility.”
Steve Shedlock
Incident Response Team Lead SEI“Everything you want to know is as easy as querying a database. It’s fantastic.”
Security Engineer
E-learning Company“Product works great, is inexpensive, zero Dev complaints about slowing down systems (IYKYK), and they've added every feature I've asked for.”
Security Operations Manager
Business Services Company"Clean interface, very good visibility across assets, and their team is open to feedback."
Manager, Information Security
Finance Industry"A unified view from which we can quickly ask and answer security questions across our environment."
Chris Castaldo
CISO Crossbeam“A major game changer for heavily used hosts (40k requsts per second). Running safely within one of the largest cloud environments on the internet. ”
Uptycs Customer
"Uptycs simplifies investigations and saves time—about 30% per investigation.
Sean McElroy
CSO Lumin Digital“If threat actors try to evade detection Uptycs captures those events”
Security Engineer
Large Telecom Company“Blazingly fast. 0.7 seconds from execution to detection, and 1.6 seconds from execution to case management alert.”
Security Engineer
Global Payment ProcessorUptycs provides actionable runtime threat and vulnerability insights and a flexible threat hunting capability.
Uptycs Customer
Director, Information Security Financial“Monitoring containers for Exploit/Mining Activity can be easily traced compared to other apps”
Security Engineer
Telecom Company“For so many issues, our answer is ‘Go to Uptycs.’”
Director of Security Operations
Enterprise Logistics Company“Uptycs enables us to make risk-based decisions.”
Chris Castaldo
CISO, Crossbeam“We transitioned to Uptycs from an industry behemoth. We reduced costs, but more importantly, Uptycs' digs deeper for more impact.”
Computer & Network Security
Large EnterpriseResources for
the modern defender
Prepare for any challenges that lie ahead by choosing
the right tools today.
Gartner® CNAPP Market Guide
Security Observability for Productivity and Server Endpoints
ESG Report: Secure the Expanding Cloud-native Attack Surface
See Uptycs in action
Find and remove critical risks in your modern attack surface - cloud, containers, and endpoints - all from a single UI and data model. Let our team of experts show you how.
